February 26, 2020
3944
The need for safety and security guarantees for electronic embedded systems has never been stronger.As cars become more automated, we need to improve their security to protect them from hackers.The same is true for factories with lots of robots and IoT devices that need to process sensitive data
The need for safety and security guarantees for electronic embedded systems has never been stronger.As cars become more automated, we need to improve their security to protect them from hackers.The same is true for factories with lots of robots and IoT devices that need to process sensitive data
The way flash memory is used
If we look closely at the electronic systems of modern cars, we will find that flash memory is widely used throughout the vehicle.As the complexity of the system increases, we need larger volumes of code storage and data storage.All in-car subsystems, including advanced driver assistance systems (ADAS), instrumentation systems (to be merged with infotainment), drive and body systems, require embedded systems to run in real time.
All of these embedded systems require some type of flash memory for code storage and data storage.For example, figure 1 shows an ADAS subsystem that USES multiple NOR flash devices.
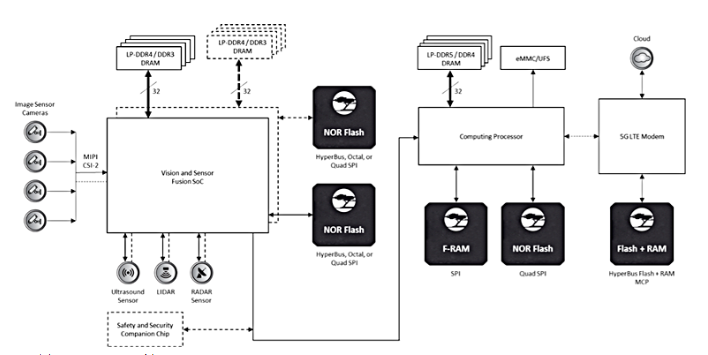
Figure1. The ADAS subsystem USES multiple NOR flashes
In today's ADAS applications, complex algorithms and artificial intelligence processes run on code and data stored in flash memory.Storage must provide failover safety and security, as system failure or malicious attack may result in serious personal injury or even death
Similar security and security requirements exist for storage solutions in industrial and network applications.In the context of increasing connectivity, hackers can break through any weak entity connected to the Internet, steal sensitive information, or use a compromised device as a springboard to launch attacks elsewhere in the network.Therefore, it is critical to build secure systems to avoid this type of attack
Secure flash storage
Flash memory vendors have been offering pure data storage for years.For these applications, durability and retention are two major indicators of flash memory quality.Security is not a requirement for this type of flash, which means that data stored on flash is either completely unprotected or protected by unauthenticated commands.
For example, some flash memory devices provide basic protection through a normal set of commands, such as non-volatile or volatile protection for sectors for programming or erasing operations, password protection for programming or reading operations, and so on.These features are good, but not good enough to withstand sophisticated attacks.If hackers have access to the flash device's bus interface, they can easily extract or modify the data on the device.
To ensure security, flash devices must protect stored code and data from multiple means of attack.The following summarizes several attacks that flash storage devices need to guard against
Man in the middle (MIM) attack
Hackers in MIM attacks often impersonate the sender of a communication channel, sending commands or messages to the other side to steal or modify data (figure 2).Therefore, it is necessary to authenticate every message between the host and the flash device.Authentication can be achieved by using the public key on the host and flash to generate the message authentication code (MAC) that accompanies the actual message.The receiver can verify the MAC before acting on the message.
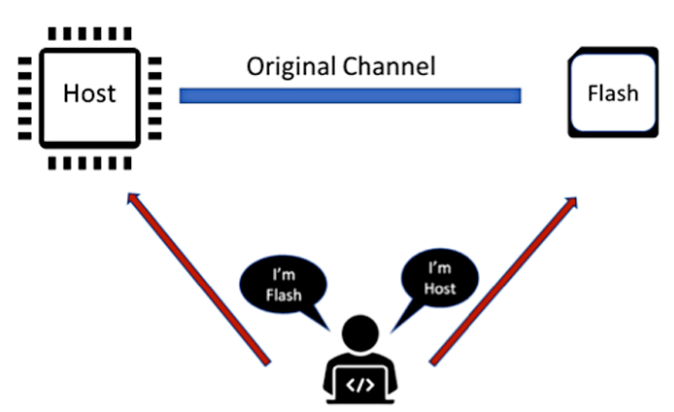
Figure 2. Man-in-the-middle attacks often mimic the channel sender of a communication by sending commands or messages with the ultimate goal of stealing or modifying data
To prevent the system from being permanently compromised if the key is compromised, you usually need to use a temporary key.The temporary key will expire after a certain time or a certain number of times.The goal is to avoid key decryption by methods such as destructive physical analysis (DPA) or other iterative attacks as much as possible
Another man-in-the-middle attack is to replay intercepted legitimate messages after a certain time.To prevent replay attacks, the host and flash devices must use an accumulator counter (the value increases with each message) to generate the MAC.Because the current accumulate counter value is different from the previous message value.Replaying the same message does not pass MAC authentication
Clone !!
Some hackers can use advanced technology to read the entire contents of flash memory chips and make money from illegal cloning.To prevent such attacks, each flash chip must have a unique device secret (UDS) that no one can read.UDS value is unique and is the real random value in each chip.There is no correlation between the UDS in one chip and the UDS in the other
UDS can be used to derive the composite device identifier (CDI), which is the basis for generating the device ID certificate defined by the TCG device identifier combination engine (DICE) specification.In general, the device also generates aliased private key public key pairs for all keys exported with the host, based on CDI.This eliminates the need to expose the device ID's private key.
With UDS and DICE flows, since UDS are physically impossible to clone, hackers cannot clone devices.
Eavesdrop !!
Passive interception is another known attack.By eavesdropping on the bus, the attacker can collect sensitive information or confidential information from the data transmitted through the bus.To protect important data, users have the option to encrypt data before sending it over the bus to a flash device and storing it.When the host retrieves data from the device, the data should also be encrypted, leaving potential hackers permanently stranded.
One might argue that the encryption approach does not require a secure flash storage solution because the host can encrypt data directly and store it in flash.Only the host can decrypt the data
However, there are some disadvantages to doing so.One is that the host cannot easily abandon the encryption key.For example, if you use KeyA to encrypt data and store it in flash memory, then the user discovers that KeyA has been compromised and needs to use a different key on the system, KeyB
At this point, the host is in a dilemma: it cannot just abandon KeyA because it needs to keep the key to decrypt the data it reads from the device.However, if KeyA is breached, users may not want to keep it forever.To use the new data encryption key, users have to take more complex measures.Erase the original encrypted data on the flash and program the flash with the newly encrypted data.The operation is not easy on the spot and carries some risks
On the other hand, if a secured flash can provide encryption and decryption, it can safely store plaintext data in its secured storage and encrypt it before sending it back to the host.If the current encryption key is compromised, the host can simply exchange the new key with the device.Keeping the data in storage intact and secure is a much simpler approach than storing encrypted data.
Safeguard Procedures !!
Provides a flexible memory architecture
In modern multicore embedded systems, multiple MCU or hardware security modules (HSM) may be able to access the same flash storage.Flash devices need to provide a flexible memory architecture that can be partitioned and configured to manage different regions through different kernels.These different areas can provide different levels of security or, when not needed at all, remove security.
By looking at the eMMC standard and the UFS standard, it is clear that there is a trend to support multiple security zones.The current eMMC standard specifies playback protected memory blocks (RPMBS).The latest UFS (v3.0) standard provides intelligent support for four RPMB partitions, which are managed by four different keys.Such memory architecture flexibility is more appropriate in a multi-core SoC environment
Provides fast and secure startup
Many embedded systems store startup code in flash memory.This is partly because of the need for a quick start, such as an automotive subsystem that needs to process the CAN message within 100ms of a power reset (POR).Not only does the system need to start securely (that is, verify the startup code), it also needs to start quickly.This poses a higher challenge for embedded designers
Typically, when the storage is run and the (SnD) mode is downloaded, the host reads the boot loader from flash and maps it to RAM for execution.However, to start safely, you need to verify the entire boot loader code to ensure its credibility.This process takes time on the MCU.Secure flash storage can provide boot load authentication, greatly reducing startup time
Secure flash devices can use internal secure hash functions to check the boot loader and provide the host with hash values for verification.If the hash value does not change, the boot loader has not been tampered with and can be safely used for startup
Provide secure firmware wireless updates (FOTA)
For modern embedded applications, on-site upgrade is a necessary function.By remotely upgrading a system's firmware or software, manufacturers can quickly resolve problems, provide new features, and improve the user experience.However, remote upgrades can also pose a security threat to the system.No one wants a hacker to use an existing update channel to run malicious firmware or software.
In addition to relying on the security provided by the CPU, the internal security engine of the flash device can also significantly improve the security level of the FOTA process (figure 3).With such a security engine, the flash device that provides the boot code store can be authenticated not only by the host next to the flash device, but also by the remote cloud.In this way, end-to-end channel security can be established for firmware updates or software updates in flash
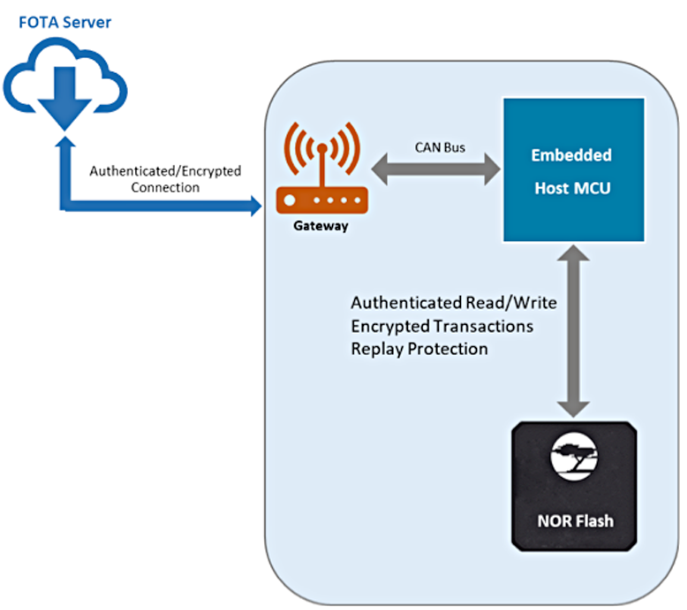
Figure 3. The security engine in the flash device helps to implement a more secure firmware wireless update process
Embedded systems used in modern automotive, industrial, and communications systems require highly secure data storage.The challenge for embedded systems designers is how to build secure systems that can withstand cyber attacks.Flash memory with integrated security features, such as Semper Flash from cypress, improves overall system security by preventing various attacks against embedded systems